Network Inventory Software
IT Inventory Management for the Whole Network
Based on the comprehensive inventory of your network, LOGINventory provides you, as an administrator, with an automated and detailed overview of all assets you need for the management of individual server systems, complex IT infrastructures, or entire data centers. Our network inventory software accompanies you optimally in the procurement, installation, configuration, operation, maintenance, and servicing of your network components and is the basis for a reliable IT documentation and software license management for your company. Also, you can easily create network diagrams with LOGINventory.
The network inventory feature as part of our IT Asset Management Software is agentless and covers Windows computers, Macs, Linux and mobile devices as well as all SNMP-enabled devices such as printers and switches. This orivides you with a complete overview of the entire hardware and software in your network.
What can be inventoried?
Test LOGINventory yourself!
Free download, ready to use in 5 minutes. Why not give it a try?
Which data does our Network Inventory Software collect?
Depending on the type of device, different data are available for evaluation. For example, a MAC address table is available for switches, but no software inventory.
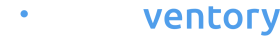
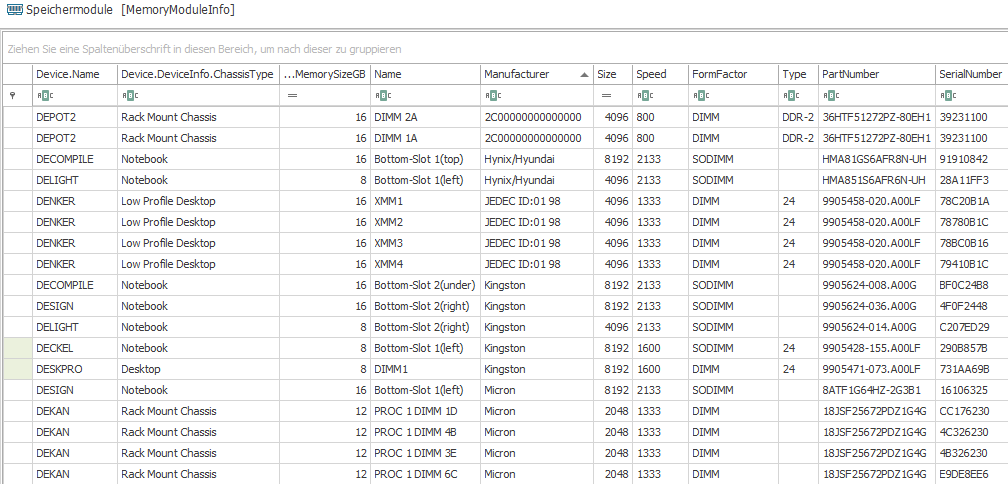
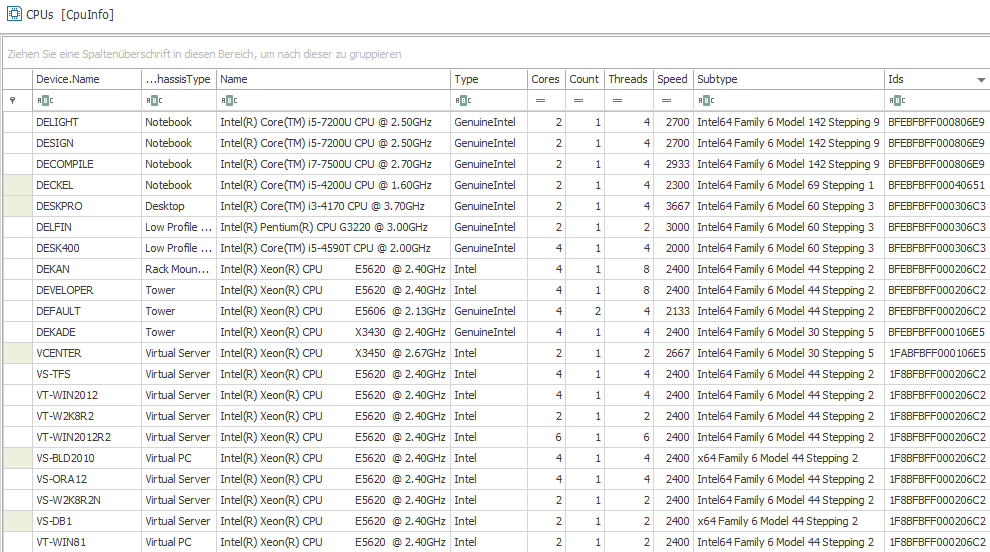
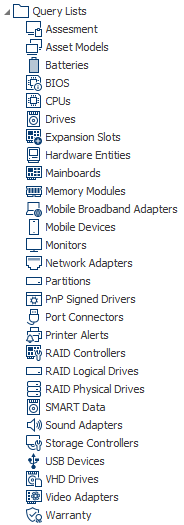
Hardware Inventory
For instance, the IT inventory of your network can provide access to the following values:
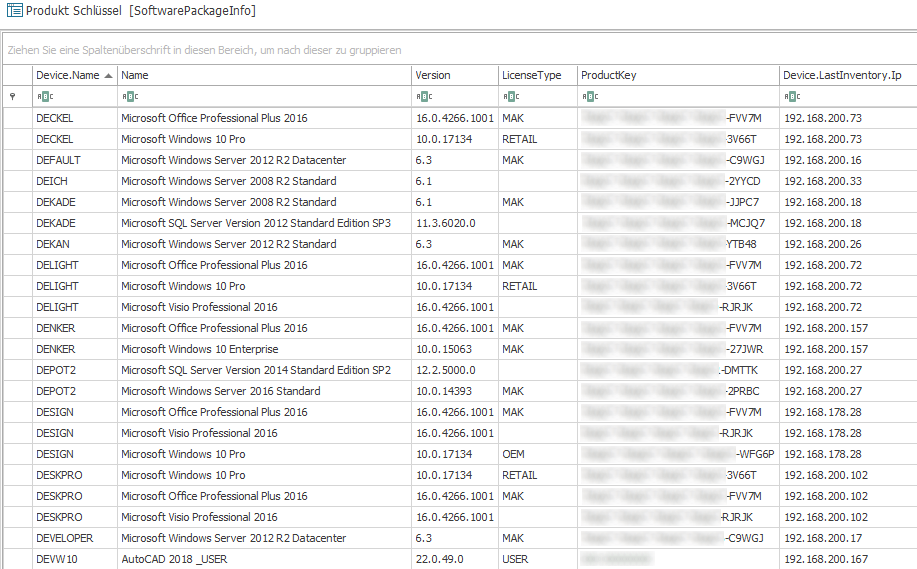
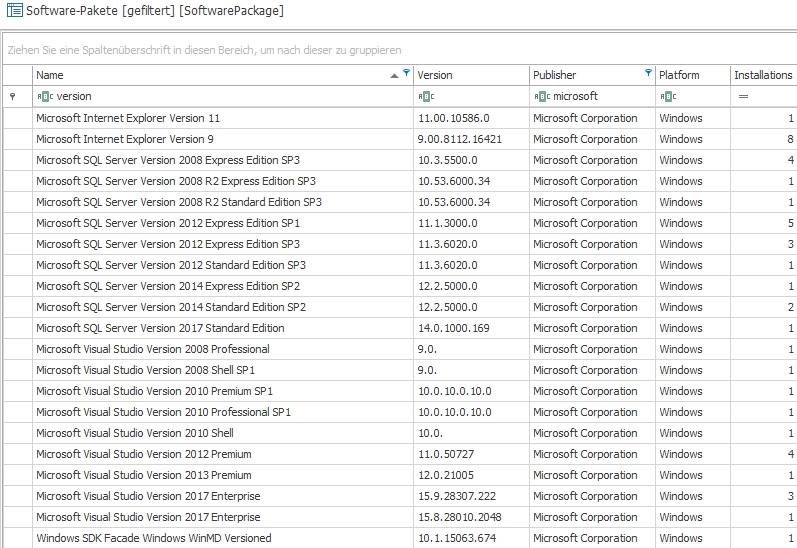
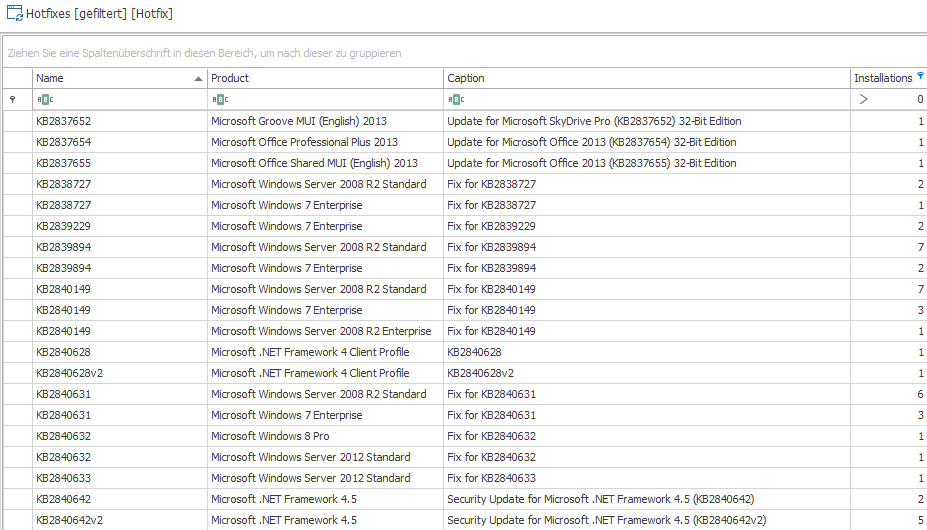
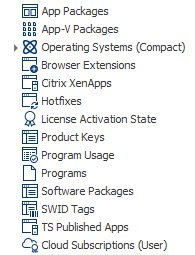
Software Inventory
By gathering data from both clients and servers, it is possible to showcase the following information pertaining to the current software in use:
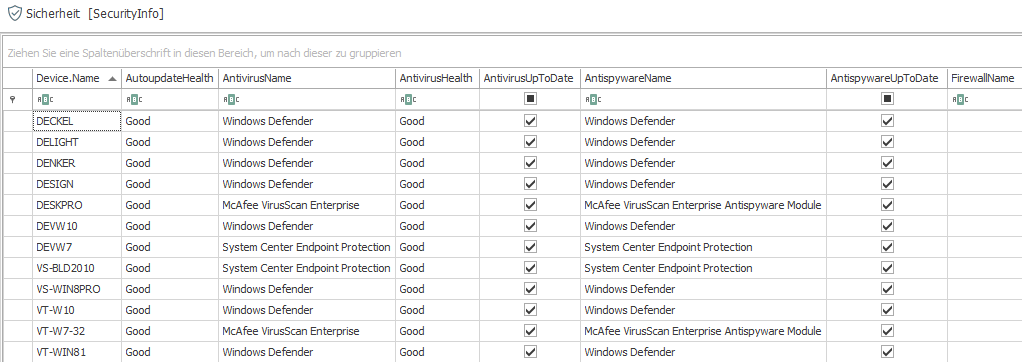
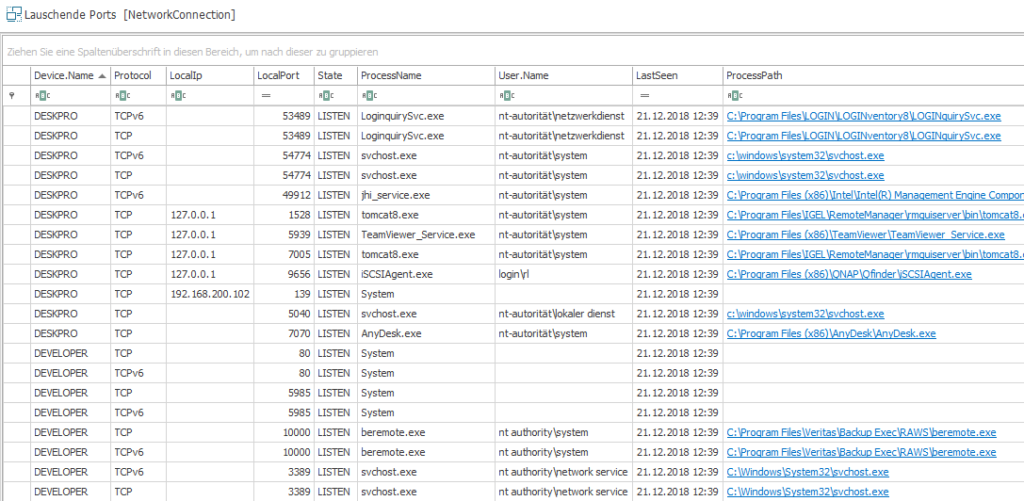
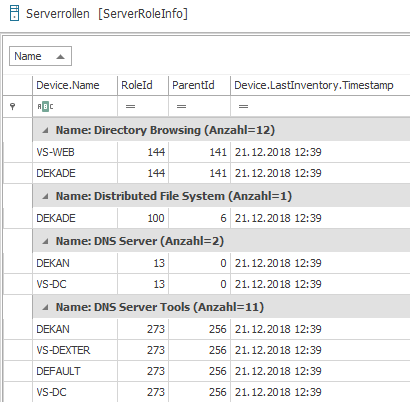
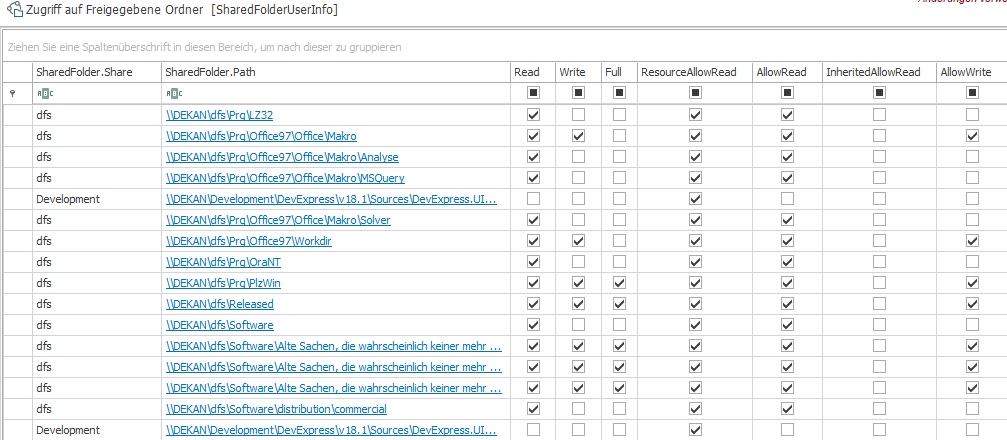
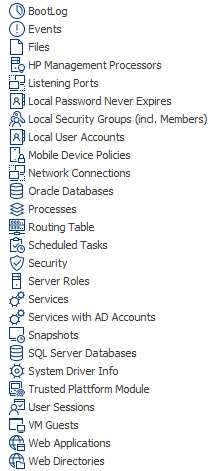
Scan of the Configuration
The IT inventory of all network components displays the status of firewall, antivirus and antispyware as well as the following data:
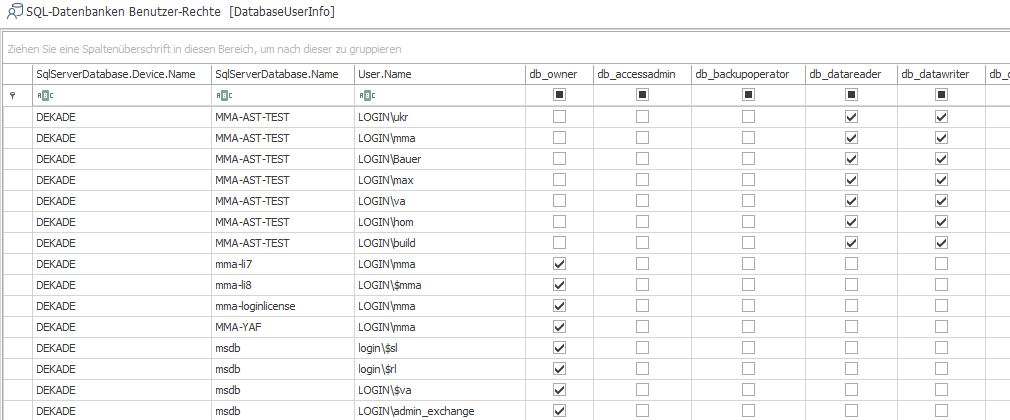
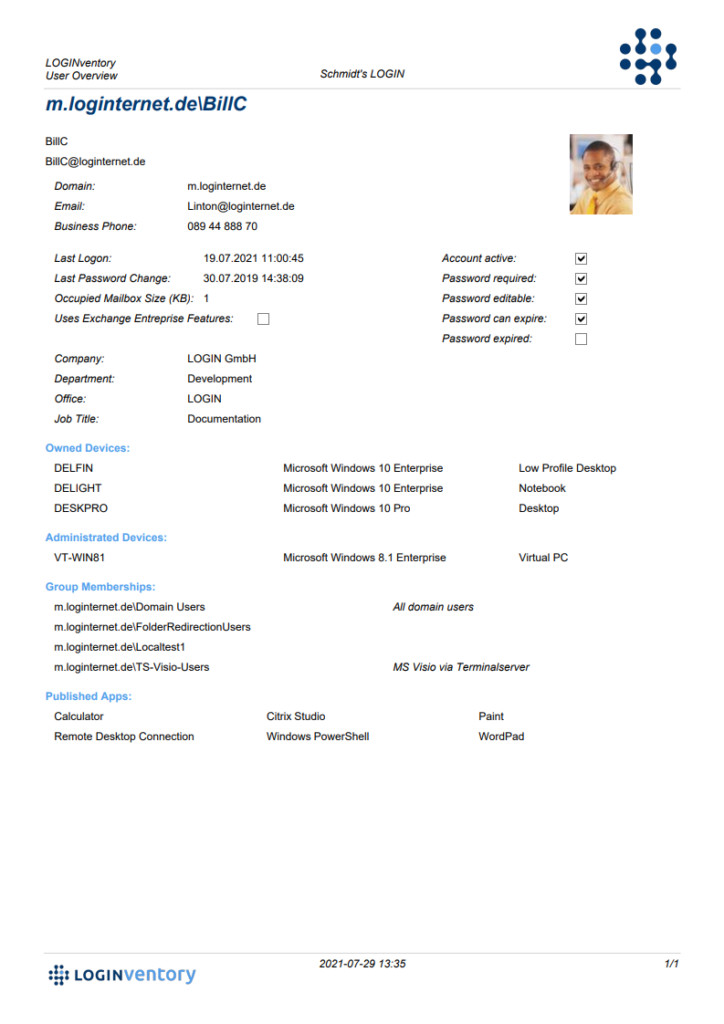
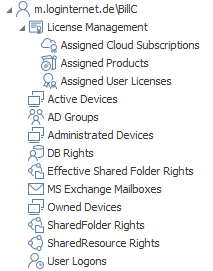
User-Related Data
LOGINventory provides a diverse range of user account-related information, significantly streamlining user management processes:
Are you interested in monitoring your network or systems with even greater precision? It’s simple; the collection process can be easily expanded and customized. For instance, you can integrate additional OIDs from SNMP devices, registry entries, or files located in specific directories into the scanning procedure. Further details about this customization are available in the manual.
How is the network inventoried?
LOGINventory presents various methodologies for gathering data, ensuring comprehensive access to all details within your company’s network for thorough evaluation. These methods are unified by a singular objective: Streamlined, automated retrieval of information from all relevant devices.

Agentless Network Inventory
LOGINventory can utilize IP address ranges to effortlessly scan the network and gather comprehensive information. For this process, the device being scanned needs to support a remote interface (like Windows APIs, SSH, SNMP), and LOGINventory must have an account stored with the appropriate permissions to access the data. These scans can be automated, meaning they run on a schedule, ensuring fully automated acquisition without any manual intervention, giving you peace of mind.
IT-Inventory via Logon Script
Alternatively, data can be gathered using a logon script, eliminating the need for an agent. To achieve this, simply include the call of a scan file within the computer’s logon script. This captures computer information in the user context immediately upon user login, enabling automatic data transfer without additional manual steps.
Agent-Based Inventory of Laptops Outside the LAN
To efficiently inventory laptops used by field staff in off-site locations lacking a VPN connection, LOGINventory can catalog these computers using an agent and subsequently transfer the data securely, for instance, through HTTPS.
Computer Inventory via USB Stick
Ideal for one-time data capture: Simply run a scan file copied onto a USB stick to swiftly scan devices in just around 30 seconds. Subsequently, import the gathered data into the respective database for convenient access and evaluation purposes.
Would you like to know more? Take a look at the manual and see all the details!
IT Inventory and User Management: Issue and Return of Devices
LOGINventory offers the possibility to automatically generate an individual label including QR code for all devices, including IT peripherals and accessories, and to document the issuing or return of the device to/from a specific user.
Each asset managed within LOGINventory is assigned a unique inventory number. This number serves as the foundation for generating an exclusive web address for each device through a QR code.
LOGINventory streamlines the automatic creation of printable QR code labels in widely-used formats. All you require is a label printer to affix these labels onto devices. Additionally, these labels are customizable and can be personalized by incorporating your company logo.
These QR code labels are easily scannable using a smartphone or tablet without the need for an app. Upon scanning, the opened page displays various device details. During device handouts, users can be selected to whom the device is allocated. Furthermore, there are fields available to include notes and a signature section where users can sign using their finger. Completing the handover process via the designated button records a lifecycle entry within LOGINventory, capturing the entered data and signature on the device. Moreover, the device’s owner (main user) is updated accordingly. The return process operates in a similar manner.
How to Analyze Inventory Data?
Efficiently managing your company’s network relies on swiftly accessing the necessary data. Our network inventory software offers multiple evaluation options designed to facilitate quick and easy access to the information you require.
You can find out in detail how to carry out IT documentation with LOGINventory here.
Test LOGINventory yourself!
Free download, ready to use in 5 minutes. Why not give it a try?